Russian website streaming hundreds of cameras in Canada, experts warn your connected devices could be at risk | Globalnews.ca

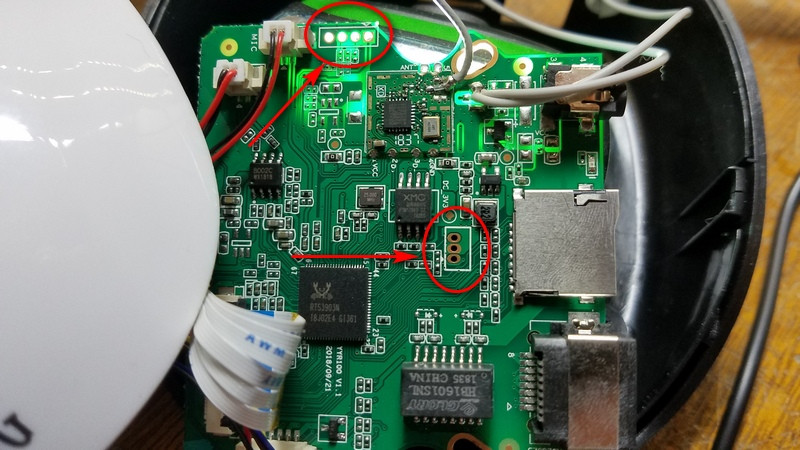
Amazon.com : POE Camera, SV3C 4MP POE IP Security Surveillance Camera Outdoor(Wired), IR Night Vision 65-100ft, Motion Detection, H265, H264, IP66 Waterproof, Metal Shell, Onvif Conformant, Support Blue Iris, RTSP : Electronics
/cdn.vox-cdn.com/uploads/chorus_asset/file/22357957/Screen_Shot_2021_03_09_at_5.07.30_PM.png)
Security startup Verkada hack exposes 150,000 security cameras in Tesla factories, jails, and more - The Verge